Rogue AI Agents: The Hidden Risk in Agent-to-Agent Systems
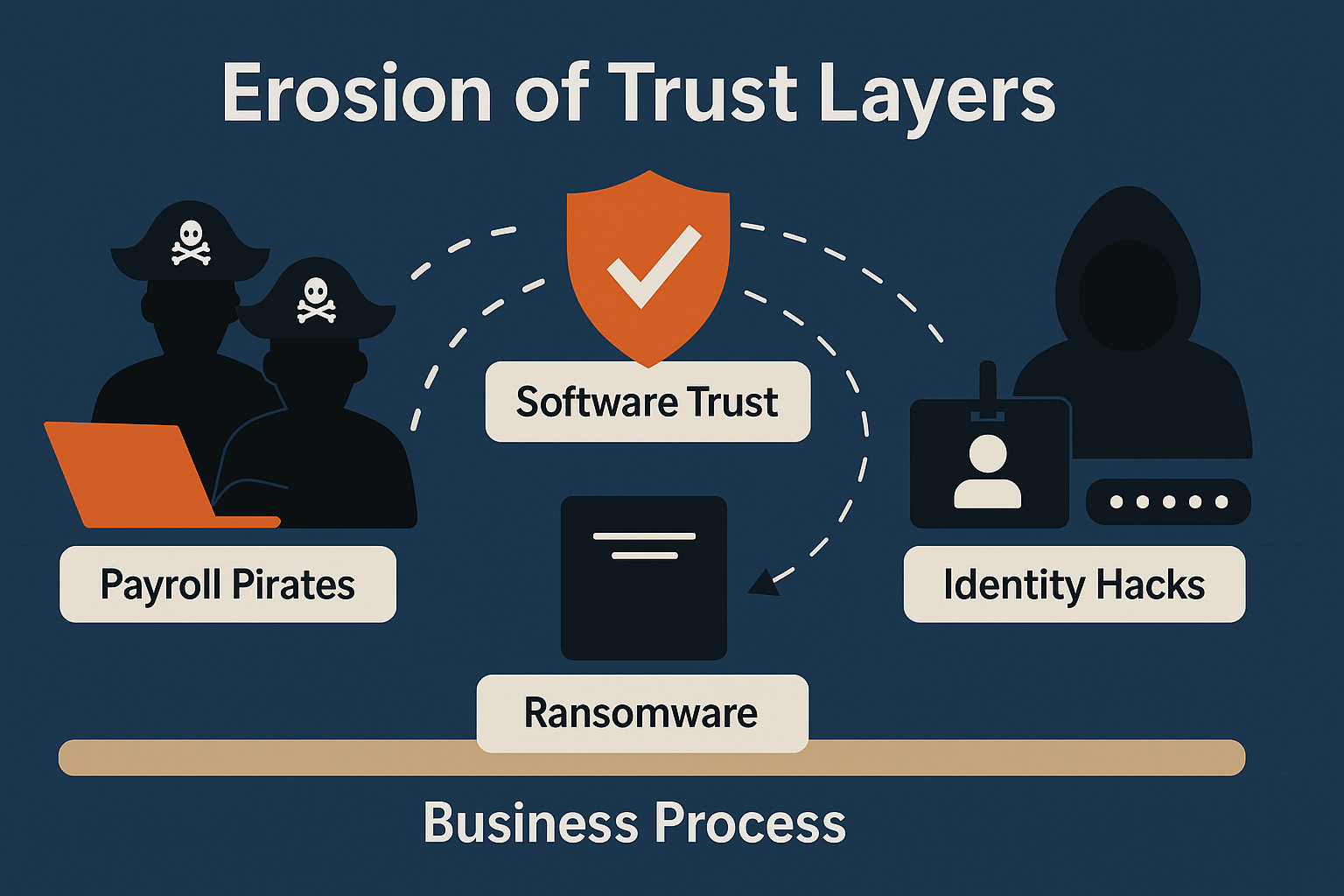
Click here to view/listen to our blogcast. AI is no longer limited to chatbots or research tools. In modern business systems, AI “agents” increasingly communicate directly with other agents, sharing data, scheduling actions, and even completing transactions automatically. These interactions save time, but they also open a new kind of vulnerability: agent session smuggling, where […]