Microsoft Issues Triple Cybersecurity Warning: Payroll Pirates, Certificate Abuse, and Identity Hacks
Click here to view/listen to our blogcast.
Last week, Microsoft released three separate cybersecurity warnings that reveal how cybercriminals are evolving their tactics to attack organizations from multiple angles at once.
The threats include:
- Payroll Pirates – cybercriminals hijacking HR systems to redirect employee paychecks.
- Azure Certificate Abuse – ransomware gangs signing fake Microsoft Teams installers with valid certificates.
- Identity Hacks – a 32 % surge in password-based account compromises.
Each of these represents a different piece of the same puzzle – attackers exploiting trust in our accounts, in our software, and in our people.
1. Payroll Pirates Targeting HR and Payroll Platforms
Microsoft’s first alert warned of a threat group called Storm-2657 criminals stealing university employees’ pay by changing bank details inside HR SaaS platforms such as Workday.
How it works:
- Victims receive phishing emails designed to steal credentials and MFA codes.
- Attackers log into HR systems and change payroll routing to attacker-controlled accounts.
- They create inbox rules to delete confirmation messages from the HR system, so the victim never sees the alerts.
Why it’s dangerous:
- The breach uses legitimate credentials, bypassing antivirus or firewalls.
- It directly results in financial loss rather than data theft.
- Victims often discover it only when paychecks go missing.
Protect yourself:
- Use phishing-resistant MFA (security keys or authenticator apps).
- Require dual approval for payroll or banking changes.
- Monitor for mailbox rules that delete or forward HR notifications.
2. Ransomware Gangs Exploiting Azure Certificates
Microsoft also disrupted a campaign by Vanilla Tempest (Vice Society), which distributed ransomware using more than 200 stolen or abused code-signing certificates, including some from Azure’s Trusted Signing service.
What happened:
- Attackers created fake Microsoft Teams installer sites like teams-download[.]buzz.
- The fake installers were digitally signed, tricking users and endpoint security tools.
- Once installed, they dropped a backdoor that deployed Rhysida ransomware.
Why it matters:
- Signed malware appears “trusted” and bypasses many defenses.
- The abuse of legitimate certificates undermines one of the core pillars of cybersecurity trust.
- It shows that even major cloud ecosystems like Azure can be weaponized.
Mitigation steps:
- Always download software from official Microsoft domains.
- Maintain an inventory of certificates and monitor for unauthorized use.
- Enable EDR tools that analyze behavior, not just digital signatures.
3. Identity Attacks Surge by 32 % in 2025
Microsoft’s Digital Defense Report 2025 revealed a worrying trend: identity-based attacks increased by 32 %, with over 97 % involving password abuse.
Key findings:
- Credential stuffing and password reuse remain the top attack vectors.
- Infostealer malware and fraudulent help-desk resets are rising sharply.
- Weak or reused passwords are still the easiest way into most organizations.
Best practices:
- Enforce strong password policies and ban password reuse.
- Disable legacy authentication methods (POP, IMAP, basic auth).
- Adopt Zero Trust principles. Never assume a user or device is safe just because it’s on your network.
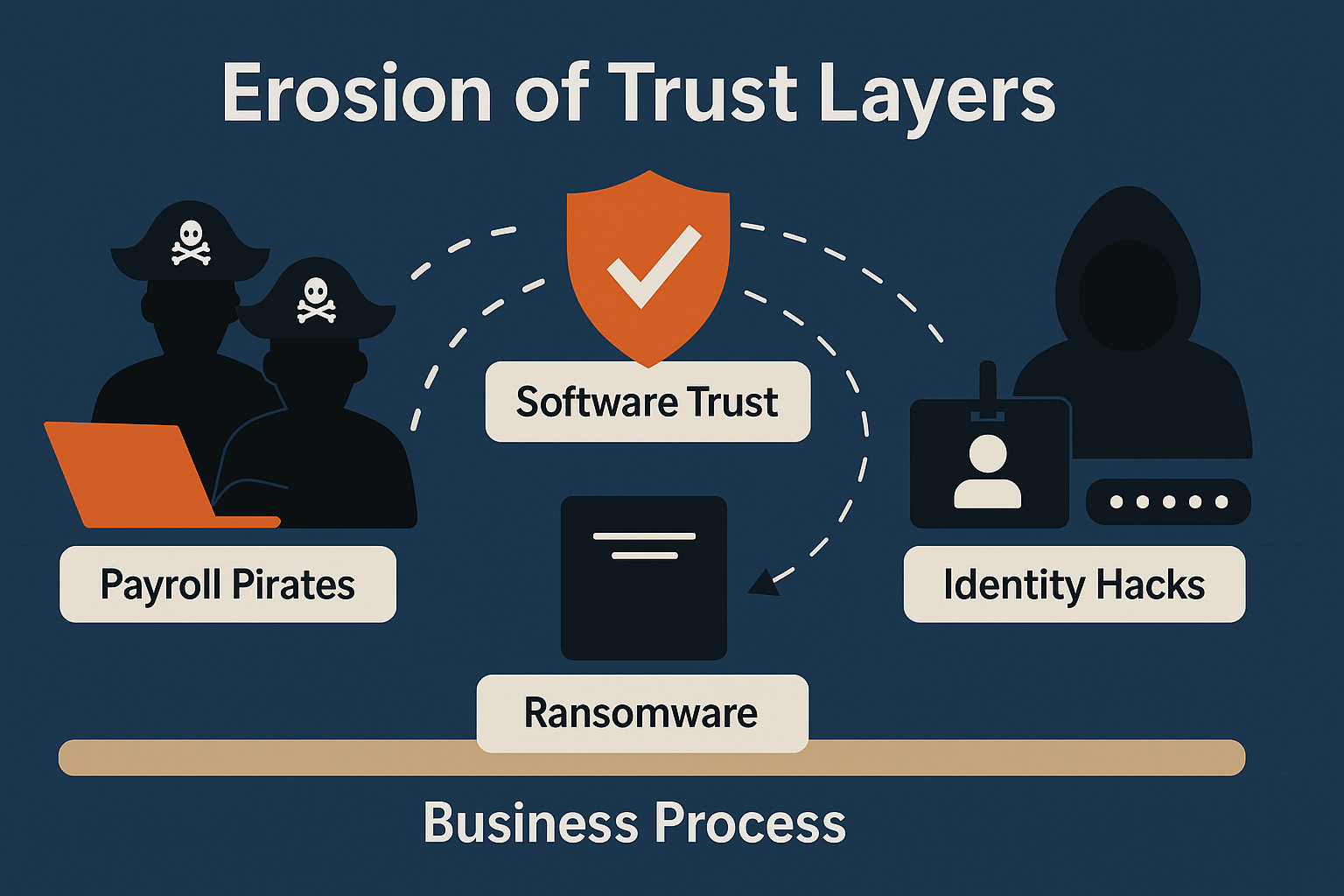
Common Thread: Erosion of Trust
These three stories highlight a single truth: attackers are eroding the layers of trust that modern IT depends on:
| Targeted Trust Layer | Example Attack | Result |
| User Identity | Phished credentials & MFA codes | Account takeover |
| Software Trust | Signed fake installers | Ransomware deployment |
| Business Process | HR/payroll tampering | Direct financial theft |
The convergence of these tactics means even small organizations are at risk if they rely solely on “check-the-box” security controls.
How CDML Can Help
At CDML Computer Services, we help businesses protect their people, data, and processes from evolving threats like these. Our managed cybersecurity and compliance solutions include:
- Microsoft 365 Business Premium with Defender for 365 and email encryption.
- SonicWall firewalls with advanced threat protection and monitoring.
- LastPass Enterprise password management and multifactor authentication.
- Employee security-awareness training to reduce phishing risk.
- Comprehensive incident-response and disaster-recovery planning.
- 24 × 7 monitoring and patch management through our managed service agreements.
Our proactive approach ensures you have the right policies, tools, and response plans before an incident occurs, not after.
Final Thoughts
Cybercriminals no longer rely on a single tactic, they exploit every layer of digital trust: credentials, software signatures, and business workflows. Microsoft’s triple warning should serve as a wake-up call for all organizations: security isn’t just about technology, it’s about vigilance and verification at every level.
If you’re unsure whether your systems could withstand one of these attacks, schedule a security assessment with CDML Computer Services today.
We’ll help you identify gaps, close vulnerabilities, and ensure your business stays protected no matter what the next wave of attackers brings.
Stay safe. Stay informed. Stay compliant.

📞 Contact us here: https://cdml.com/contact/
📚 Read more on our blog: https://cdml.com/blog-2
📺 Listen to our blogcasts: https://www.youtube.com/@CDMLComputerServices