Silent Threats: Why FileFix Attacks Should Be Your Top Security Concern
Click here to view/listen to our blogcast.
Cybercriminals never stop innovating, and a new social‑engineering tactic called FileFix is setting off alarm bells! First revealed in June 2025, FileFix leverages our trust in everyday Windows workflows using the clipboard and File Explorer to execute malicious commands making it dangerously stealthy.
What Is FileFix?
At its core, FileFix is a modern twist on an earlier attack known as ClickFix, where users are deceived into pasting harmful code into the Windows Run dialog. FileFix takes that premise a step further by hiding malicious commands in what appears to be a harmless file path in Windows File Explorer.
How the attack unfolds:
- The victim receives a phishing link or visits a compromised site.
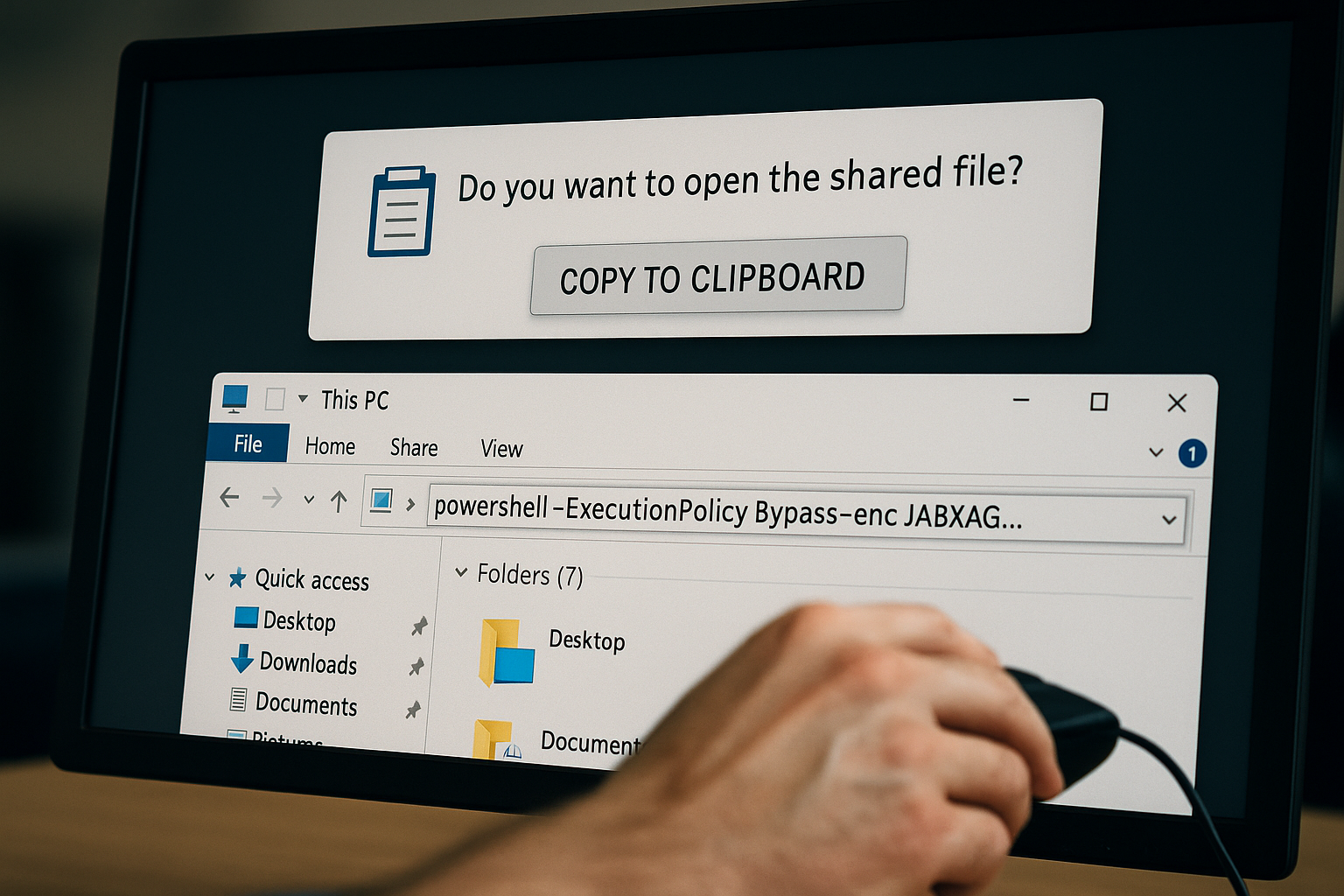
- A seemingly legitimate prompt appears, telling them to “open the shared file.”
- JavaScript silently copies a crafted PowerShell command into their clipboard.
- The user is told to open File Explorer, press Ctrl+L, paste what looks like a file path, and hit Enter.
- Instead of navigating to a folder, the command runs fetching malware, installing RATs, or worse.
Because this method exploits trusted OS behavior and doesn’t trigger obvious alerts, antivirus and endpoint defenses often fail to detect it.
Why It Matters
- Rapid adoption: Check Point reported FileFix in real‑world use within two weeks of its emergence, employing it to deliver remote access Trojans and ransomware like Interlock.
- High stealth: By hijacking familiar actions and bypassing “Mark of the Web” protections, FileFix evades typical malware defenses.
- Wide impact: Used in campaigns targeting financial, healthcare, education, local government, and more.
How You Can Protect Your Organization
Users are often the weakest link but also your first line of defense. Raise awareness:
- Never paste unverified clipboard content into File Explorer or Run dialogs.
- Train staff to stop and confirm before acting on any instructions involving Open File Explorer, clipboard actions, or pasted paths.
- Verify prompts: Legitimate support instructions rarely require manual PowerShell or clipboard commands.
From a technical standpoint, consider implementing these measures:
- Disable risky features: Use Group Policy to restrict Run and explorer-based command execution.
- Restrict PowerShell: Enforce signed-script execution or disable clipboard-triggered scripts.
- EDR/XDR detections: Monitor unusual clipboard activity from browsers or Explorer and flag any PowerShell execution triggered by such events.
- Clipboard control: Limit navigator.clipboard.writeText calls from untrusted webpages.
Does Using Browsers Like Brave Help?
Using a privacy-focused browser like Brave can help reduce exposure to FileFix-style attacks:
What Brave does well:
- Blocks JavaScript and clipboard access from unknown sites by default.
- Reduces phishing risk with built-in protections and HTTPS enforcement.
- Limits fingerprinting and deceptive popups that attackers use to mimic legitimate prompts.
What Brave can’t do:
- It can’t stop users from pasting malicious commands if they’ve already been tricked.
- It doesn’t control the Windows clipboard or File Explorer, where the real damage happens.
Conclusion: Brave is a smart part of a defense-in-depth strategy, but not a standalone solution. User training and system hardening remain essential.
How CDML Can Support Your Defenses
CDML specializes in helping organizations strengthen their human and technical shield:
- Tailored training & awareness programs: Equip your team to recognize FileFix-style deception.
- Endpoint hardening services: CDML consultants configure GPO/registry settings to disable risky OS features and reinforce PowerShell restrictions.
- Advanced threat detection: Our XDR services continuously monitor for suspicious Explorer/clipboard activity and anomalous PowerShell launches.
- Incident readiness: If a FileFix attempt does occur, CDML provides expert forensic analysis, threat mitigation, and rapid remediation to minimize impact.
By integrating CDML services, your organization gets proactive protection and incident response designed specifically for today’s social-engineering attacks.
Final Thoughts
FileFix is deceptively powerful because it exploits user trust and routine behavior. Your best defense:
- Train your users
- Harden your systems
- Monitor activity continuously
- Partner with experts like CDML
Security isn’t just a software issue – it’s a human issue. And CDML is here to help you navigate both.
Stay safe. Stay informed.

📞 Contact us here: https://cdml.com/contact/
📚 Read more on our blog: https://cdml.com/blog – 2
📺 Listen to our blogcasts: https://www.youtube.com/@CDMLComputerServices